NEWARK, N.J. (AP) — A British man accused of hacking into U.S. government computer networks and stealing sensitive and confidential information was arrested in England, and U.S. prosecutors said they will attempt to have him transferred to New Jersey. Lauri Love, of Stradishall, England, has been charged with hacking into agencies including the U.S. Army,…
LLNL Licenses Tool to Improve Government Computer Network Security
Government agencies, along with state and local governments, could receive a helping hand from a computer network security tool developed by Lawrence Livermore National Laboratory (LLNL) computer scientists and engineers. The LLNL software-based technology, known as the Network Mapping System (NeMS), has been licensed to Cambridge Global Advisors, a Washington, D.C.-area strategic advisory firm. “We…
Stories You Shouldn’t Miss — July 3-9
Here they are — the top most visited stories from the past week. A spyware peddler suffers a major hack; experimental artificial heart is a success; 8-minute video of Rover Opportunity’s Epic Mars Marathon; astounding new mosaic image of our Sun’s surface, and a series of intriguing spots along Pluto’s’ equator are all among the…
Milan-based Hacking Team appears to get Hacked
LONDON (AP) — An Italian surveillance company known for selling malicious software used by police bodies and spy agencies appears to have succumbed to a damaging cyberattack that sent documents and invoices ricocheting across the Internet. Hacking Team’s Twitter account appears to have been hijacked late on July 5, 2015, posting screenshots of what were…
NIST 2015 – 6th Annual Conference & Expo
NIST 2015 – 6th Annual Conference & Expo November 3-4, 2015 Paradise Point San Diego, California Attendee Registration Call For Papers (Presentations) will be released in mid-July The 6th Annual Conference & Expo will take place from November 3 to 4, 2015, in San Diego, CA. It is sponsored by the National Initiative for…
RAID: Alive or Dead?
Is RAID dead or alive? Are erasure codes replacing RAID for data protection? We present these questions, because some storage vendors promote RAID, while others promote erasure codes. Looking at how vendors are marketing data protection in their products, it almost appears that there is a battle between RAID and erasure code technology and that…
Extremely Sophisticated Criminals access Tremendous Amount of IRS Data
WASHINGTON (AP) — More than 100,000 taxpayers have had their personal tax information stolen from an IRS Web site as part of an elaborate scheme to claim fraudulent tax refunds. The information was stolen from an online system called “Get Transcript,” where taxpayers can get tax returns and other tax filings from previous years. In…
With One False Tweet, Computer-based Hack Crash Led to Real Panic
BUFFALO, NY — A false tweet from a hacked account owned by the Associated Press (AP) in 2013 sent financial markets into a tailspin. The Dow Jones Industrial Average dropped 143.5 points and the Standard & Poor’s 500 Index lost more than $136 billion of its value in the seconds that immediately followed the post.…
Advancing Security and Trust in Reconfigurable Devices
A research team at the Georgia Tech Research Institute (GTRI) is studying a range of security challenges involving programmable logic devices — in particular, field programmable gate arrays (FPGAs). FPGAs are integrated circuits whose hardware can be reconfigured — even partially during run-time — enabling users to create their own customized, evolving microelectronic designs. They…
Bringing Cyber Threat Predictive Analytics to The Cloud
ARMONK, NY — IBM is bringing its Security Intelligence technology, IBM QRadar, to the cloud, giving companies the ability to quickly prioritize real threats and free up critical resources to fight cyberattacks. The new services are available through a cloud-based software as a service (SaaS) model, with optional IBM Security Managed Services to provide deeper…
New Pentagon Strategy Warns of Cyberwar Capabilities
PALO ALTO, CA (AP) — A new Pentagon cybersecurity strategy lays out for the first time publicly that the U.S. military plans to use cyberwarfare as an option in conflicts with enemies. The 33-page strategy says the Defense Department “should be able to use cyber operations to disrupt an adversary’s command and control networks, military-related…
Cloud Security Reaches Silicon: Defending against Memory-access Attacks
In the last 10 years, computer security researchers have shown that malicious hackers don’t need to see your data in order to steal your data. From the pattern in which your computer accesses its memory banks, adversaries can infer a shocking amount about what’s stored there. The risk of such attacks is particularly acute in…
Restoring Lost Data: 3-D Digital Laser Microscopy Creates Visual Roadmap
It can be disheartening to learn that something precious, such as a one-of-a-kind family photo, has disappeared from a scratched or broken CD or DVD. It also can become serious, dangerous and potentially costly if it happens to a disc containing criminal forensic evidence, corporate records or scientific data. But there may be a way…
MOVIA Big Data Analytics Platform
MOVIA Big Data Analytics Platform is designed to help organizations watch for important patterns in their data and generate instant alerts to users or other systems. The software enables improved prediction of trends through advanced data modeling that captures situational context, so decisions are not ‘made in a vacuum.’ It employs semantics and logical reasoning…
Mathematicians adapt Knapsack Code to take on Quantum-level Cyber Attacks
PULLMAN, WA — Mathematicians have designed an encryption code capable of fending off the phenomenal hacking power of a quantum computer. Using high-level number theory and cryptography, the researchers reworked an infamous old cipher called the knapsack code to create an online security system better prepared for future demands. The findings were recently published in…
Better Debugger: Algorithm Automatically Finds Integer-overflow Bugs
Integer overflows are one of the most common bugs in computer programs — not only causing programs to crash but, even worse, potentially offering points of attack for malicious hackers. Computer scientists have devised a battery of techniques to identify them, but all have drawbacks. Researchers from MIT’s Computer Science and Artificial Intelligence Laboratory (CSAIL)…
Once-in-a-Century: Celebrating 10 Digits of Pi on 3.14.15 at 9:26:53
An e-pi-c day is coming! On 3.14.15 at 9:26:53; the date/time will correspond to the first 10 digits of the mathematical constant pi (3.141592653). This happens only once per century — a truly once-in-a-lifetime event for most people. The mathematical constant, which is the ratio of a circle’s circumference to its diameter, can be used…
Achieving Efficient, Strongly Consistent Data Storage
One of the fundamental and open problems in computer science is effective data storage. Unfortunately, magnetic and flash storage devices alone have proven to be unreliable to guarantee data availability and survivability, due to their frequent and unpredictable failures. Replication has been the prominent technique to prevent data loss. By replication, copies of the data…
Security Gaps Discovered in 39,890 Online Databases
Due to a misconfigured open source database upon which millions of online stores and platforms from all over the world base their services, anyone had the ability to call up or modify several million pieces of customer data online including names, addresses and e-mails. According to the Center for IT-Security, Privacy and Accountability (CISPA) in…
Digital Disease Detection: Using Big Data to Detect Outbreaks
Personal information taken from social media, blogs, page views and so on is used to detect disease outbreaks, but does this violate our privacy, consent and trust? Dr. Effy Vayena from the University of Zurich and colleagues have mapped the numerous ethical challenges confronting digital disease detection (DDD) and propose a framework to address the…
Biosurveillance Gateway Supports Centralized Global Disease Response
LOS ALAMOS, NM — A new online resource, called the Biosurveillance Gateway, is in place at Los Alamos National Laboratory, providing a centralized portal for all news, information, resources and research related to biosurveillance at the laboratory. “The goal of the site is to support global disease surveillance, providing useful tools developed at Los Alamos…
Self-powered Intelligent Keyboard could Provide New Layer of Biometric Security
By analyzing such parameters as the force applied by key presses and the time interval between them, a new self-powered non-mechanical intelligent keyboard could provide a stronger layer of security for computer users. The self-powered device generates electricity when a user’s fingertips contact the multi-layer plastic materials that make up the device. “This intelligent keyboard…
Cybersecurity Expert Warns Not Enough Being Done to Prevent Highly Destructive Cyberattacks on Critical Infrastructure
Research Triangle Park, NC — Inadequate training and a culture of complacency among many owners and operators of critical infrastructure are significantly raising the risks of highly damaging cyberattack throughout the world. That’s the viewpoint expressed by Steve Mustard, an industrial cybersecurity subject-matter expert of the International Society of Automation (ISA), as well as a…
Obama Unveils Cybersecurity Proposals in Advance of State of the Union Address
WASHINGTON (AP) — President Barack Obama has said that recent cyberthreats to Sony and the military’s U.S. Central Command are reminders of the serious threats facing the nation. Obama laid out plans on January 13, 2015, as part of a push for new cybersecurity legislation that increases government information-sharing and protects businesses from lawsuits for…
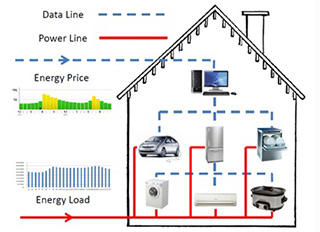
Smart Homes: Working to Prevent a Cybersecurity Nightmare
Imagine the smart home of the future. Thanks to a central controller and Wi-Fi, not only does the thermostat power up and warm or cool the house as you are heading home, smart light bulbs come on low at dusk and brighten up as the sky gets darker; your washing machine starts a load of…